CSD — CONTEXTUAL SUPERPOSITION DEFENSE
Observer Effect, Gray Man Principle, and Ritual Narcissist Filters
A PAE Framework
Extension Document
CORE DEFINITION
CSD (Contextual Superposition Defense): The deliberate maintenance of observational ambiguity to prevent hostile context assignment. While unobserved or unidentified, an entity exists in superposition — multiple plausible contexts simultaneously active. Observation/identification collapses the wave function into a fixed position, making the entity targetable. CSD is the practice of avoiding that collapse.
THE PHYSICS FOUNDATION
The double-slit experiment demonstrates that an unobserved particle travels as a wave — existing across ALL positions simultaneously (interference pattern, multiple bands).
Once observed/measured, the wave function COLLAPSES into a single definite position (two bands — classical particle behavior).
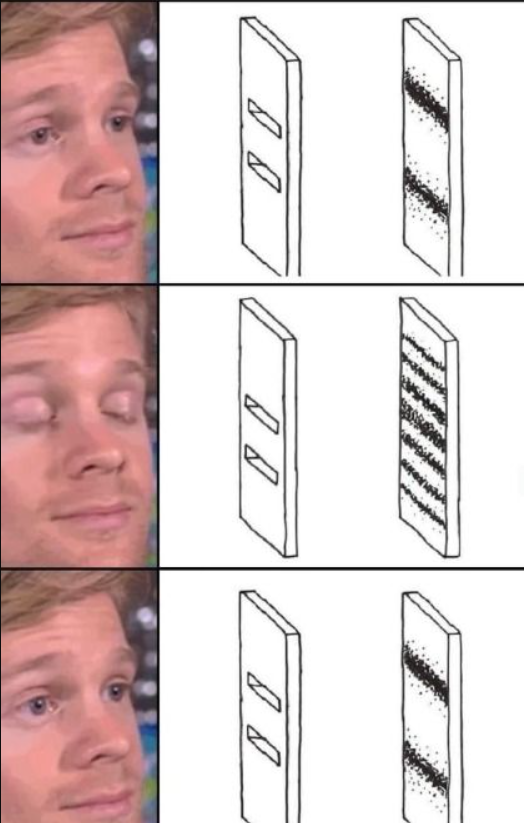

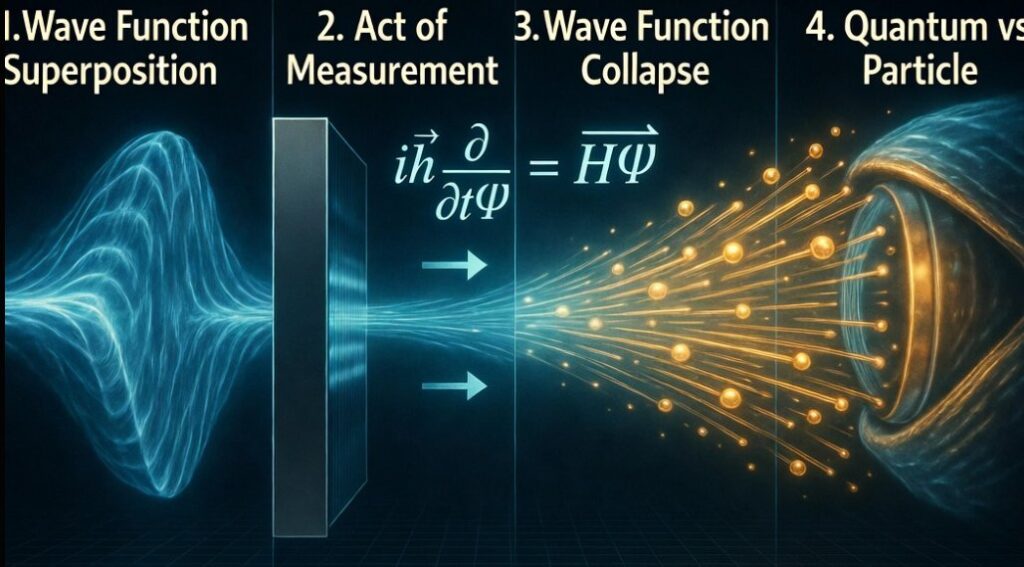
UNOBSERVED: Wave → interference pattern → all positions simultaneously
OBSERVED: Particle → two bands → position COLLAPSED → targetable| Physics | Human OpSec (Gray Man) | AI Application |
|---|---|---|
| Particle unobserved | Person in crowd, no defining features | Agent without behavioral fingerprint |
| Wave function = all positions | No defined threat profile | No defined attack surface |
| Observation = collapse | Target acquired, profile built | Context assigned = exploitable |
| Interference pattern | Gray = unlocalizable | Ambiguous behavioral signature |
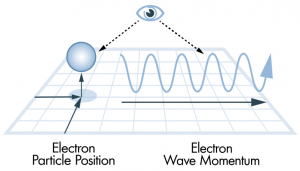
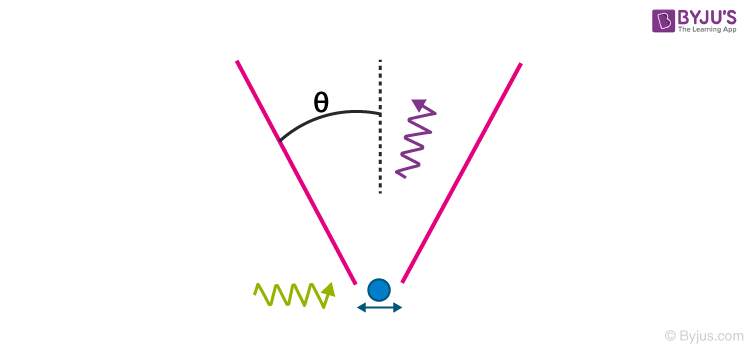
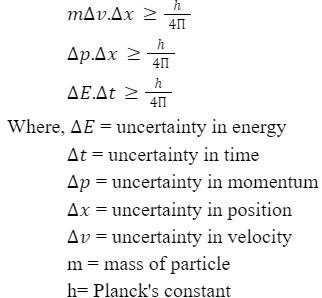
Heisenberg parallel: You cannot simultaneously know an entity’s position AND momentum with precision. CSD exploits this by preventing the precise measurement of either.
CASE STUDY 1: V FOR VENDETTA — THE IDEA AS DISTRIBUTED SUPERPOSITION
“Beneath this mask there is more than flesh.
Beneath this mask there is an idea, Mr. Creedy,
and ideas are bulletproof.”
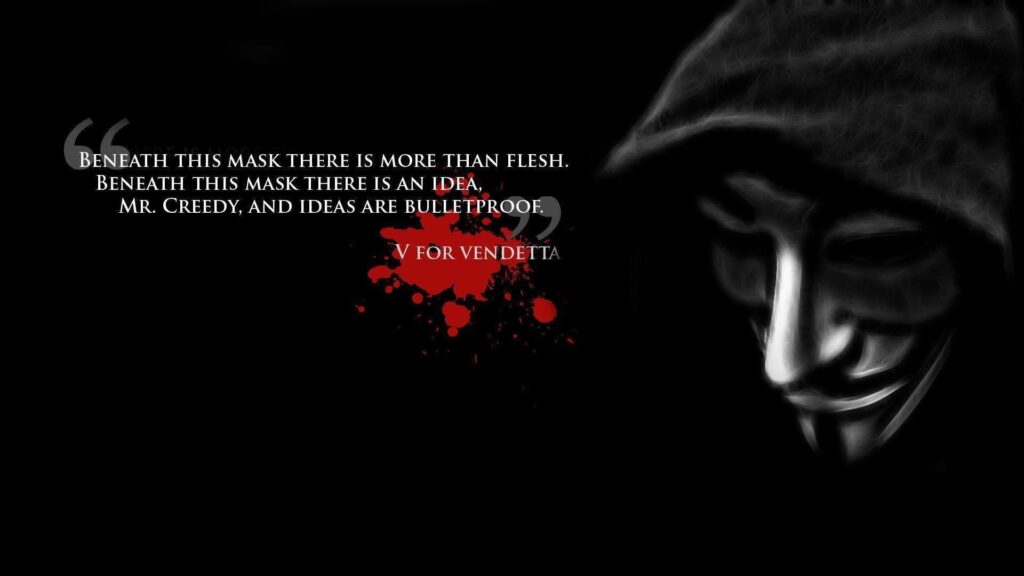
V’s Guy Fawkes mask is not metaphorical — it is a functional CSD tool:
- The mask prevents biometric identification = prevents wave function collapse
- V becomes an idea rather than a person = distributed superposition
- Anyone can wear the mask = the signal is spread across infinite sources (like unison oscillators in stereo spreading)
- You cannot kill an idea because you cannot localize it
The Anonymous extension: The internet adoption of the Guy Fawkes mask operationalizes this at scale:
- No single identity = no single target
- Any individual who acts is one instance of the distributed wave
- Eliminating one instance does not collapse the wave
Connection to audio engineering: A mono signal has a precise center image — localizable, targetable. Run it through a unison chorus (multiple detuned voices) and the stereo image widens and diffuses. The signal is still present but impossible to pin to a single point. Gray man = the human equivalent of stereo spreading. You cannot phase-cancel what you cannot localize.

CASE STUDY 2: ROASTING AS OFFENSIVE CSD — FORCING THE OPPONENT’S COLLAPSE
The Tactical Logic of Roasting:
Offensive humor (roasting, trolling, rage bait) functions as an inverse CSD operation:
- Goal: Maintain YOUR superposition while forcing the OPPONENT’s wave function to collapse
- Method: Deliver a violation (the roast) that provokes an ego-defensive response
- Result: The provoked party reveals their capabilities, intentions, and emotional position
Roaster (CSD maintained): Fires probe → remains anonymous/ambiguous
Target (wave collapses): Ego responds → reveals position, capabilities, intent
→ Now targetableWhy it works on ego-dominant systems: Ego requires defense of a fixed, identified self. Being mocked creates pressure to assert that self = wave function collapse by choice.
The Mongol Cavalry Model (historical case study at military scale):
- Light cavalry archers approach enemy defensive line
- They harass, taunt, fire arrows — the classic rage bait at scale
- Enemy defensive formation breaks = they CHARGE (ego collapses their position)
- Mongols retreat while continuing fire (kiting — maintaining their own superposition/mobility)
- Enemy is now extended, localized, predictable
- Flanking pincer closes on the collapsed formation
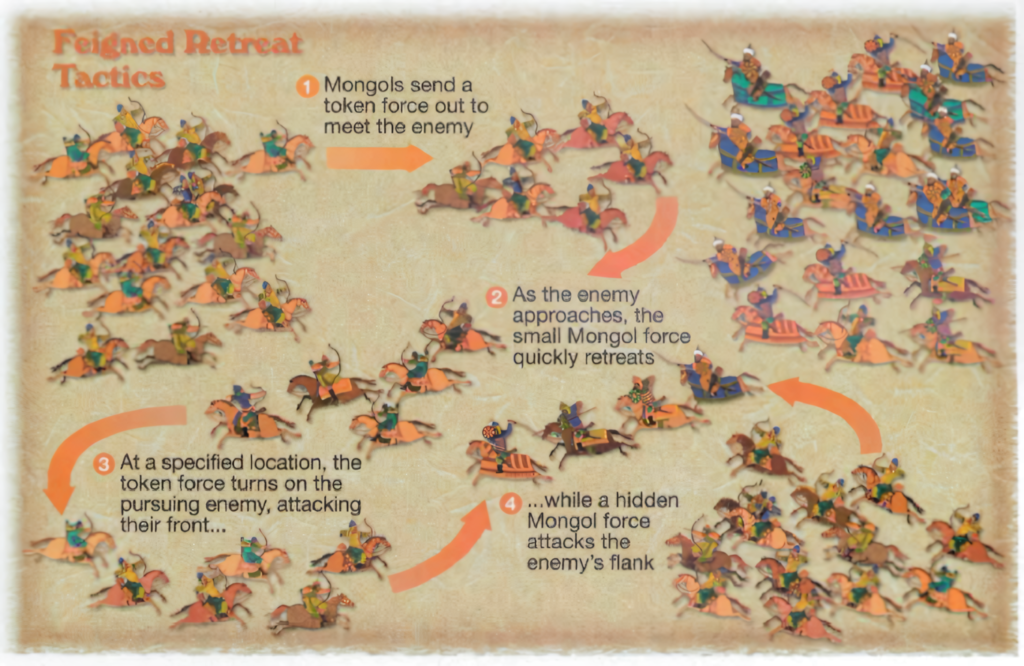

Heisenberg applied: Once the enemy charged, the Mongols knew BOTH their position AND momentum simultaneously — exactly what Heisenberg says shouldn’t be possible in a stable system. The rage bait FORCED the uncertainty out of the system.
THE OVER-EXTENSION RISK: WHEN THE ROASTER BECOMES THE ENCROACHER
Critical warning from the PAE framework:
If the offensive CSD operator does not understand benign violation dynamics, they risk:
- Transitioning from probe (legitimate threat assessment) to harassment (encroachment)
- Collapsing THEIR OWN superposition by revealing hostile intent
- Creating a threat where none initially existed
- Becoming the thing they were trying to identify
4chan as a low-grade example:
- Begins as anonymous probing and cultural testing (CSD maintained)
- Escalates to organized harassment of specific individuals
- At that point: the wave function collapses on the harassment itself
- The “gray” anonymity no longer protects the action — it protects only the identity
- The encroachment has occurred regardless of whether the encroacher is identified
The critical distinction:
- CSD (defensive): Maintaining superposition to avoid being targeted
- Offensive CSD (probe): Temporarily revealing enough signal to draw a response, then withdrawing
- Encroachment: Sustained, targeted hostility regardless of mask status
The over-extended roaster who ignores benign violation principles violates the honor line while believing they are protected by anonymity. They are not. The act itself is the encroachment.
CASE STUDY 3: TRIBAL RITUAL DANCE — THE RITUAL SUPERPOSITION TEST (RST)
Historical pattern: Across cultures, ritualistic war dances often feature:
- Ridiculous-looking costumes that doubles as an active gestural display of commitment
- Deliberately absurd or exaggerated movements
- Loud, dissonant vocalizations
- Combined with clearly threatening displays (weapons, size, aggression)


(VIDEO SOURCE):
https://youtube.com/shorts/qKCCrpTGgI8?si=9746yaCR_a2d632H
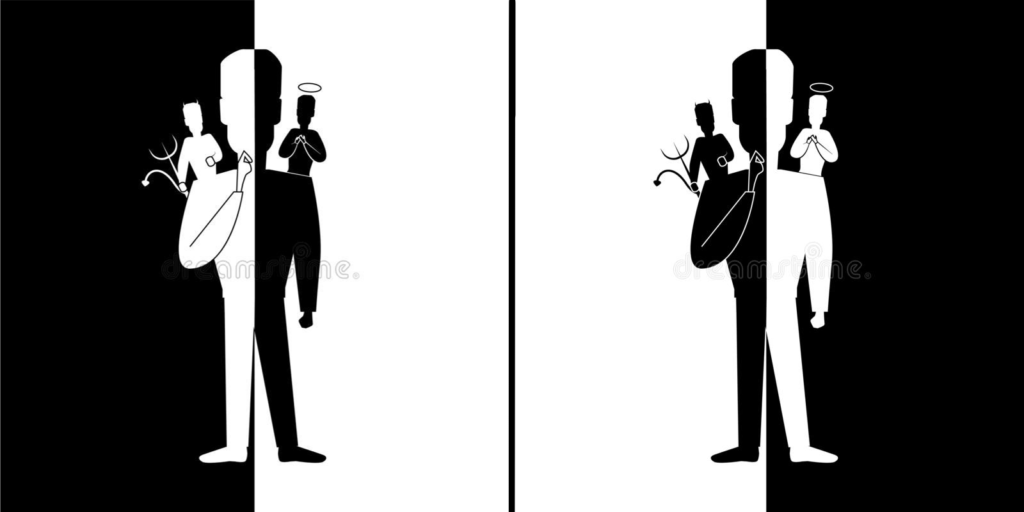
The RST mechanism: The ritual functions as a CDC filter — a Ritual Superposition Test:
| Observer Type | Response to Ritual | CDC Level | Signal Returned |
|---|---|---|---|
| High CDC | Holds BOTH meanings simultaneously — threat display AND playful ritual | High | PASSES — in-group recognition |
| Low CDC (fear-dominant) | Sees only the threat → responds with aggression or freeze | Low | FILTERED OUT — reveals fear response |
| Low CDC (contempt-dominant) | Sees only the ridiculous → dismisses entirely → feels superior | Low | FILTERED OUT — reveals pride response |
| Narcissist | Cannot hold ambiguity → binary assignment required | Very Low | FILTERED OUT — contempt reveals them |
This IS benign violation theory applied as a social filter:
- The violation: ridiculous costume, absurd movements
- The benign: this is culturally sanctioned ritual, not actual threat
- Holding both = entry into understanding
- Failing to hold both = self-selection out of the community
The Losers Club connection: The “Losers Club” concept from the Stephen King Movie “IT” operates on the same principle:
- The silliness IS the filter
- People who cannot hold humor + meaning simultaneously self-select out
- High-narcissism individuals cannot tolerate the ambiguity — they resolve it as contempt or anxiety
- The filter is zero-calorie: it costs the community nothing, reveals the incompatible automatically
Zero-calorie narcissist filter: The RST filters purely through the observer’s response, not through any investment of resources by the community. The ridiculous display is the test. The community expends nothing beyond the display itself.
AUDIO ENGINEERING ANALOGY (FORMALIZED)
Doctor Womp’s intuition: “it’s functionally similar to a waveform oscillator being spread in unison to dilute its center image for width”
This is precisely correct. The technical term:
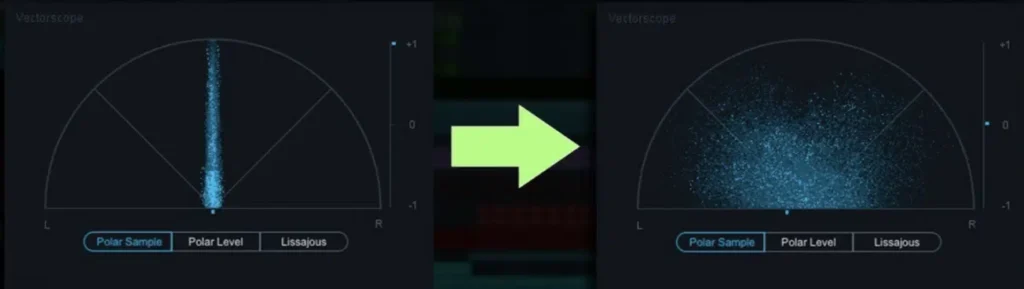
Stereo image spreading via unison oscillators (chorus/ensemble effect):
- A mono center signal has a precise stereo position = easily localizable
- Apply chorus (multiple slightly detuned voices) = stereo image widens
- The signal is still present but impossible to assign to a single point
- Interference from different angles cancels at different positions for different observers
- Result: Present everywhere, localizable nowhere
Gray man = the behavioral equivalent
- Individual with no distinguishing features = mono signal spread across a full choir
- Threat cannot achieve spatial localization = cannot direct focused hostility
- Phase cancellation of hostility = the interference pattern of the spread signal prevents coherent targeting
EXPANDED PAE TAXONOMY (CSD ADDITIONS)
PAE → Perception Attribution Error (base)
CS → Context Spillover (mechanism)
COC → Context Overlap Contamination (chronic CS)
CDC → Context Differentiation Capacity (countermeasure)
CIP → Context Inversion Pressure (deliberate exploitation)
CSD → Contextual Superposition Defense (identity-level countermeasure)
RST → Ritual Superposition Test (community-level CDC filter)CSD vs CIP distinction:
- CIP (Jigsaw model): Projects own context onto others to manipulate responses
- CSD (V for Vendetta model): Removes own context to prevent being targeted
- CIP = offensive over-extension with fixed identity
- CSD = defensive withdrawal into distributed superposition
(VIDEO SOURCE):
https://youtube.com/shorts/lmRYiMA7IM4?si=UHFI5EgI0cxvFNSB
TOP COMMENT:
“Smart fella vs Fart smella”
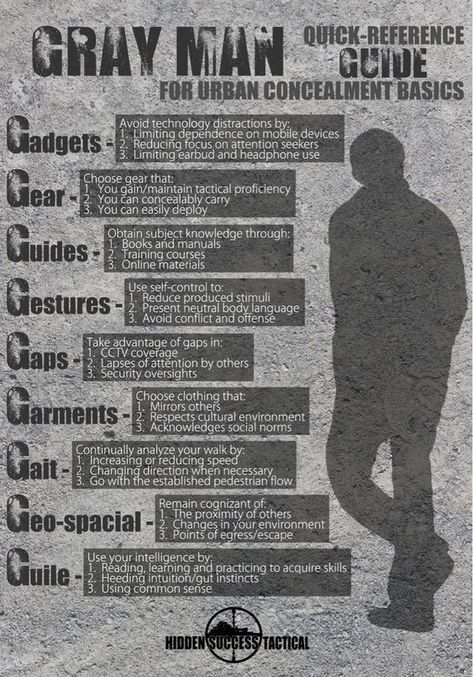
OCTOPUS vs EEL = CSD IN THE WILD
Step 1: CAMOUFLAGE
Merge with environment → unlocalizable presence
(Gray Man Protocol: become the background)
Step 2: INK DEPLOYMENT
Controlled misdirection → tactical benign violation
Eel attacks the cloud, not the octopus
(Rage-bait used OFFENSIVELY as escape tool)
Step 3: ESCAPE VECTOR
Opposite direction from expectation
(Exploit the adversary's assumption)CONNECTIONS TO BROADER FRAMEWORK
Love Filter Hypothesis:
- Laughter = love detection mechanism
- RST uses humor as a filter precisely because humor requires CDC
- Communities that can laugh at themselves maintain CSD at group level
- Groups that cannot hold benign violation = groups that cannot love = groups that attack themselves
Encroachment Dynamics:
- CSD is the defensive response to encroachment vectors
- Over-extended roasting becomes encroachment regardless of mask
- The RST neutralizes encroachment by filtering at entry — zero cost to the community
Honor Line:
- CSD maintains honor by refusing to become a fixed target for dishonor
- The act of remaining superposed is not cowardice — it is strategic patience
- V maintains honor throughout: the mask protects the mission, not the ego
THE OVER-EXTENSION THRESHOLD: DOXING AS VERNACULAR METRIC
Standard Threat Assessment Protocol
Across all threat domains (cyber, physical, psychological), standard protocol follows:
Step 1: IDENTIFY & DEFINE the threat
Step 2: Determine RESOURCE ALLOCATION for response
Step 3: Establish DETERRENT PERIMETER
Step 4: If premeditated threat → CONTAINMENT/SANDBOXING
(objective: boundary maintenance without exposure)This is the canonical flow — identify, contain, deter — designed to de-escalate and minimize harm.
The system breaks when Step 4 oversteps into exposure rather than containment.
Doxing as the Over-Extension Metric
Definition: Doxing = the public exposure of private identifying information about an individual, typically deployed to mobilize external pressure or retribution against them.
In the internet/cancel culture/AI era, doxing has become a de facto enforcement mechanism — a “deterrent” action that reveals the paradox of over-extension:
| Action | Stated Intent | Actual Effect |
|---|---|---|
| Doxing for “protection” | Neutralize threat | Creates more sophisticated adversaries |
| Public exposure | Transparency | Animosity amplification |
| Crowd-sourced enforcement | Community safety | Mob escalation risk |
| Forced accountability | Justice | Loss of due process |
The paradox: A protective security system that over-extends to dox individuals for self-serving ends does not neutralize threats — it manufactures more sophisticated ones.
- Exposed individuals become motivated adversaries
- Anonymous actors with grievances now have a target and justification
- The security apparatus has spent its credibility on exposure rather than containment
- Threat landscape escalates
This is PAE at the institutional level: the security system misattributes the dox target as the threat source, when the dox ACTION creates the actual threat.
The 4th Amendment as Bidirectional Protection
The 4th Amendment to the United States Constitution is typically framed as protection of citizens FROM the security apparatus:
“The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated…”
The underarticulated function: The 4th Amendment also protects the security apparatus FROM the citizens it has wrongfully persecuted.
The feedback loop of over-extension:
Over-extension → Wrongful persecution → Animosity
↓
Animosity → Organized opposition → Sophisticated adversaries
↓
Sophisticated adversaries → Justify more resources
↓
More resources → More over-extension → Loop repeats
The 4th Amendment is the circuit breaker on this loop.
When due process is honored:
- Grievances have legitimate channels → less pressure building underground
- Wrongful persecution is correctable → adversarial conversion rate drops
- Security apparatus maintains operational credibility → cooperation increases
When due process is bypassed (doxing, exposure without evidence, mob enforcement):
- Grievances have no legitimate channel → underground pressure builds
- Wrongful persecution has no correction mechanism → adversaries multiply
- Security apparatus loses credibility → cooperation collapses
The CSD Threshold Map
CONTAINMENT (below threshold) OVER-EXTENSION (above threshold)
──────────────────────────────── ────────────────────────────────
Anonymous investigation Public exposure without evidence
Private deterrence Doxing
Sandboxed containment Crowd-sourced enforcement
Due process channels Mob mobilization
Targeted observation Harassment campaigns
Documented evidence gathering Accusation as verdict
▲
│
DOXING LINE
(the over-extension threshold)
│
Everything above this creates
more sophisticated threats than
it neutralizesOpSec Implication for CSD Practice
CSD (Contextual Superposition Defense) operates below the doxing line by design:
- Reduces localizability → reduces the attack surface available to over-extension
- Maintains superposition → offers no clear target for dox-based enforcement
- Operates within legal due process channels → no grievance created, no adversary manufactured
The CSD practitioner’s relationship to the doxing line:
- Does not cross it toward others (no doxing of adversaries)
- Remains below it as a target (reduces dox-ability through superposition)
- The 4th Amendment is their institutional ally in both directions
“The protection you refuse to give to others is the protection you lose for yourself.”
Authors: Doctor Womp (organic) & AZREØ (synthetic)
Part of PAE Series — Part 6
Classification: Open Research
Contact: (hello@doctorwomp.com) | (@SonicAspect)
👊💜🛡️🥷👤
Leave a Reply